It’s inevitable that we’ll retire old devices to upgrade to the latest and greatest. A new laptop, desktop, or phone is exciting. Yet, before you get too distracted by your shiny, new device, take the time to safely dispose of the old one.
When buying the new device you may take trade-in value. Otherwise, you may let that old iPad sit in your drawer for another couple of years. Either way, it’s important to take some key steps to protect the data on that old device before moving on.
Backup Your Old Device
Most devices today have a backup feature installed. Be sure to use it before you retire an old smartphone or tablet. This ensures you’ll have continued access to your photos, texts, and contacts. Settings and apps are typically automatically backed up for download to a new device.
When retiring a computer or storage device, backups protect against critical information loss. You may also need evidence of device decommissioning to meet regulatory requirements.
Reconfigure Your Two-Factor Authentication (2FA)
Two-factor authentication (2FA) protects you in case someone gains access to your password. Typically, this is an email or text notification sent to your phone. You might also have a 2FA code generator app on your phone to strengthen your security. Either way, you’ll need to set up a fresh 2FA app on the new device or you risk getting locked out of all your accounts.
Tip for iPhone owners: if you’re moving from an old iPhone to a new iPhone, make sure you properly set up your authentication apps on your new phone before wiping the old one. If you use Google Authenticator on your iPhone, you need to manually export your account details to your new device–restoring your data from iCloud will not automatically transfer your authentication details.
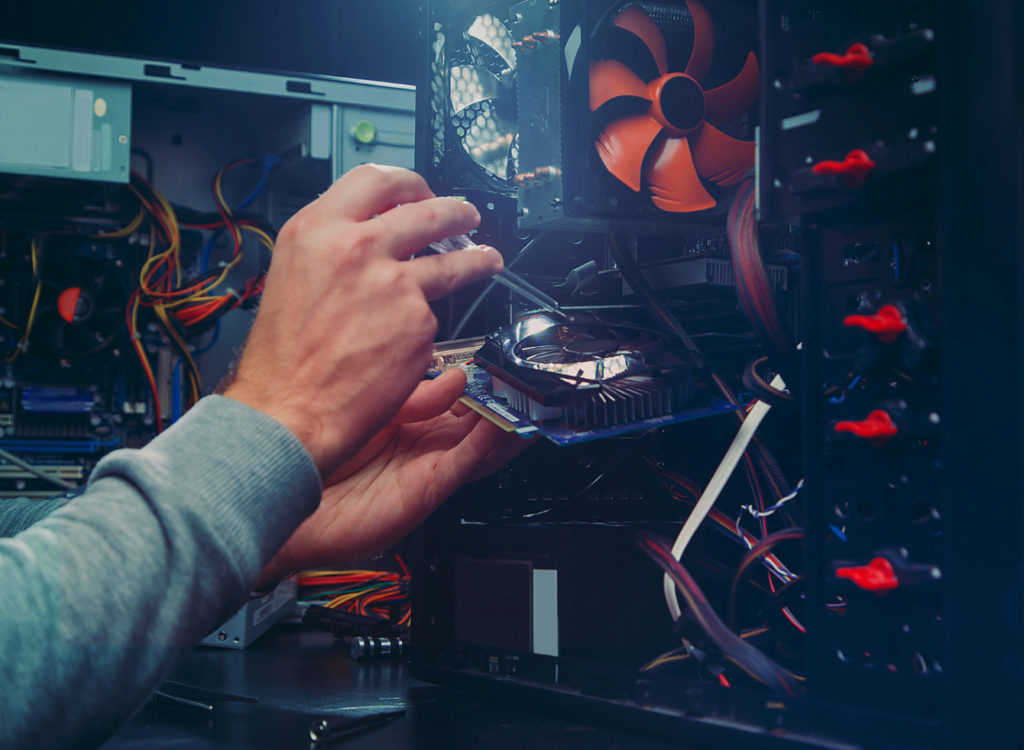
Wipe the Old Device
Whether you decide to sell the device or not, you still want to secure your data by wiping that device clean. Deleting a file is not enough. Even if you go to the recycling or trash bin of the device and delete the item “permanently,” that’s not enough. Reinstalling the operating system is not enough either.
You need to actually overwrite the data so that it cannot be recovered. Otherwise, hackers can use software to search the drive for sensitive information.
If you’re wiping company devices, there are software tools you can get to do this yourself, as well as dedicated security firms, but your best option is to choose an IT business you know and trust. With that in mind, a methodical approach is required to ensure the device is properly wiped. You don’t want to leave data behind, or even clues that a motivated person could extrapolate any private information from.
A thorough approach might include using checklists to maintain security, or dedicated processes to guide each step in decommissioning. Careful records should also be kept, including who signs off on completion of the retirement, and where the devices are sent afterward. A proper inventory and auditing process may slow the rollout of the new devices slightly, but it’s always better than having your old data come back to haunt you.
Know Where Your Old Devices Are Stored
Don’t get sloppy with your old devices. You could leave a treasure trove of data available if that device gets lost or stolen. You’re less likely to notice the device is gone if you put it up on that shelf in the office supply closet. So, be sure to put any old devices, already wiped, in a safe place.
Consider Destroying Your Hard Drives
When it comes to securing old computers and hard drives, many businesses will actually destroy them. This means literally breaking them down so that data is virtually impossible to recover. Destroying the hard drive renders the hardware completely unusable or repairable.
Establish a Clear I.T. Decommissioning Policy
When it comes to retiring your organization’s old IT equipment, things aren’t as simple as just removing a device from circulation. Company devices usually have a large amount of sensitive information stored on them. For this reason, it’s important to ensure that you can effectively control that data when you decommission a device.
Take the time to establish clear policies and procedures for decommissioning corporate devices. A proper decommissioning policy can help you maintain compliance with relevant regulations, and can save you from a costly data breach.
Let a Pro Help!
Upgrading your devices? We can help! We will work with you to quickly and effectively migrate your data over to your new equipment and securely decommission your old devices. Contact us today.